Malware analysts have found multiple samples of a new malware toolkit that can collect sensitive files from systems isolated from the internet. They call it Ramsay and there are few known victims to date.
Ramsay has not been publicly documented until today. It lands on a victim computer via a malicious RTF file and scans removable drives and network shares for Word documents, PDF files, and ZIP archives.
Three variants found
Researchers at cybersecurity company ESET found one Ramsay sample on the VirusTotal scanning platform, uploaded from Japan.
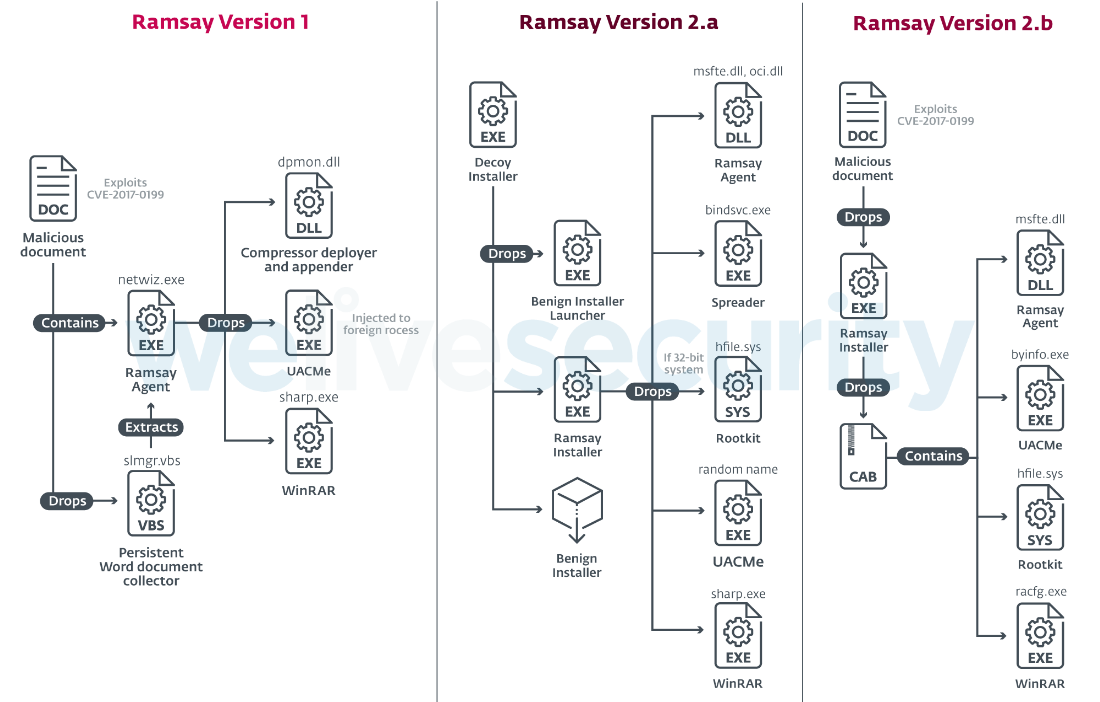
At least three variants of this malware exist, though: v1, v2.a, and v2.b. Based on the compilation timestamps, Ramsay v1 is the earliest one, from September 2019, and is also the least complex.
The other two samples (v2.a and v2.b) are more elaborate and appear to be compiled on March 8 and March 27, respectively. Both come with a rootkit component but only 2.a also has spreading capabilities.

ESET malware researcher Ignacio Sanmillan says that there is sufficient evidence indicating that Ramsay framework is still under development and that the delivery vectors are still to be refined.
In technical analysis published today, the researcher notes that the less complex versions of the malware are dropped by malicious documents exploiting CVE-2017-0199 and CVE-2017-11882, two vulnerabilities that allow executing arbitrary code.
In another attack vector delivering the more refined Ramsay v2.a, the malware posed as an installer for the 7-zip file compression tool.
The spreader component in this version is highly aggressive, Sannmillan said, to the point that it can infect any portable executable present on targeted drives.
The logical assumption for this behavior is that the attacker may want to ensure proliferation to a larger number of victims.
The lack of this functionality in the other versions of the malware could indicate that the attacker needs stricter control of distribution in the targe network, the researcher said. It could also hint at targeting a specific air-gapped system and not the entire network.
Ramsay’s purpose is to steal files from a compromised host. All variants analyzed by ESET collect all Microsoft Word documents on the file system of the target computer; newer ones will also search for PDF files and ZIP archives on network drives and removable drives.
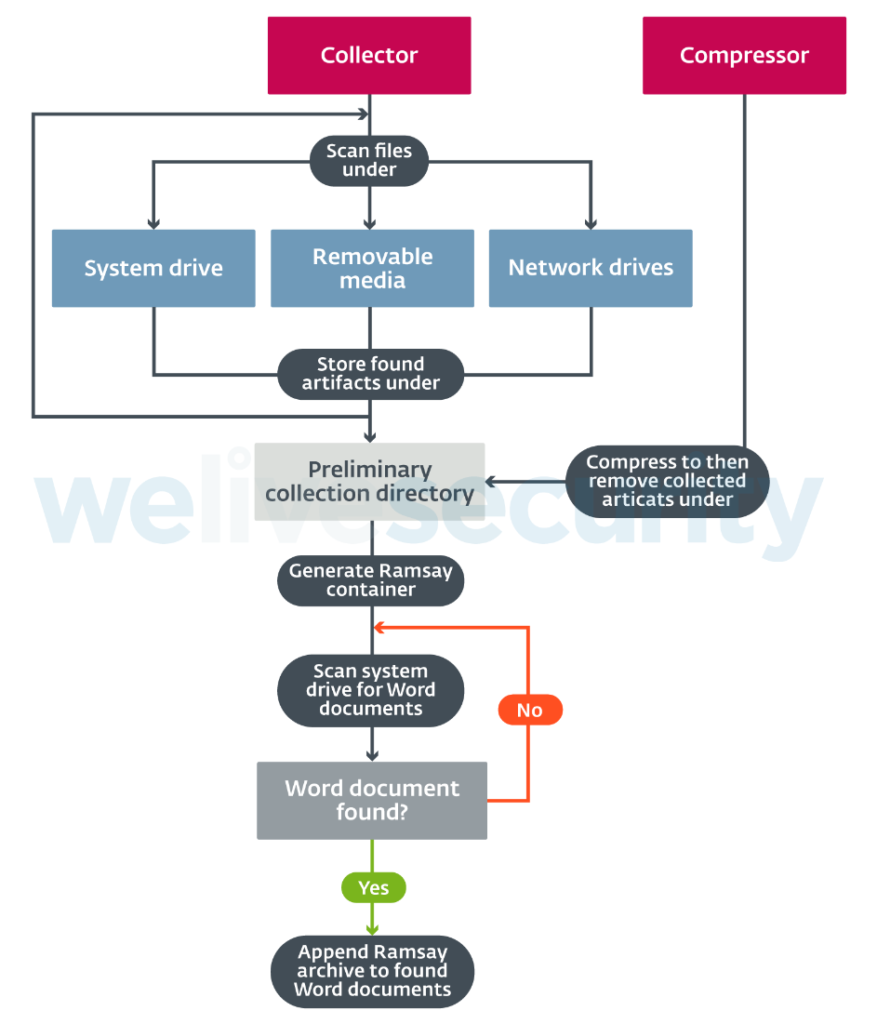
Files collected this way are encrypted with the RC4 cipher and compressed with WinRAR, dropped by Ramsay installer. A container artifact is then generated to make it easier to hide them on the system and to simplify extraction.
“Ramsay implements a decentralized way of storing these artifacts among the victim’s file system by using inline hooks applied on two Windows API functions, WriteFile and CloseHandle” – ESET
The artifact containing the stolen data is added at the end of a benign Word document. To make everything look normal to the naked eye, a footer section is appended. The resulting document looks and behaves like a valid file that can be opened in Microsoft Word.
Exfiltration possibilities
ESET’s research covers only the part of Ramsay framework that spreads to other computers, steals files, and prepares the data for the taking.
Since Ramsay is targeting air-gapped systems that are cut off from the wider internet, the threat actor cannot communicate directly with victim systems to extract stolen data or get commands.
Sannmillan says that the malware scans the local filesystem, network shares, or removable drives for special control files that contain instructions from the attacker.
This means that another Ramsay component exists to exfiltrate data and to deliver commands to the local implant.
“We did not see those two communications in action (data exfiltration or command execution), and in fact we don’t have a sample of the Ramsay exfiltrator tool, which we imagine exists in some way” – Ignacio Sannmillan
One way the attacker could do it, the researcher told us, is to compromise a computer connected to the internet that is used by an employee to transfer files to a host on the air-gapped network.
Such as system would intermediate the communication with the disconnected computer via a removable drive that is used on both. A special control file could instruct Ramsay to copy on the drive the already prepared Word file
When the drive connects to the computer with internet access, the file is exfiltrated. which is then exfiltrated.
Another scenario is for the attacker to have physical access to the infected system. After planting Ramsay and leaving it running for a while, they can return and grab the files.
Murky evidence
Despite finding artifacts previously seen in the Retro backdoor used by DarkHotel advanced group of hackers, attributing Ramsay to an adversary is not possible at this time.
One clue pointing to a potential connection to Retro backdoor are several tokens present used by both malware pieces.
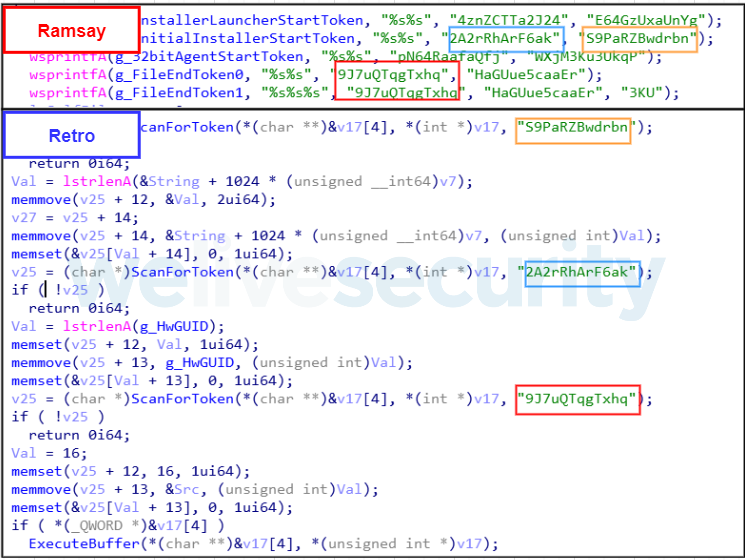
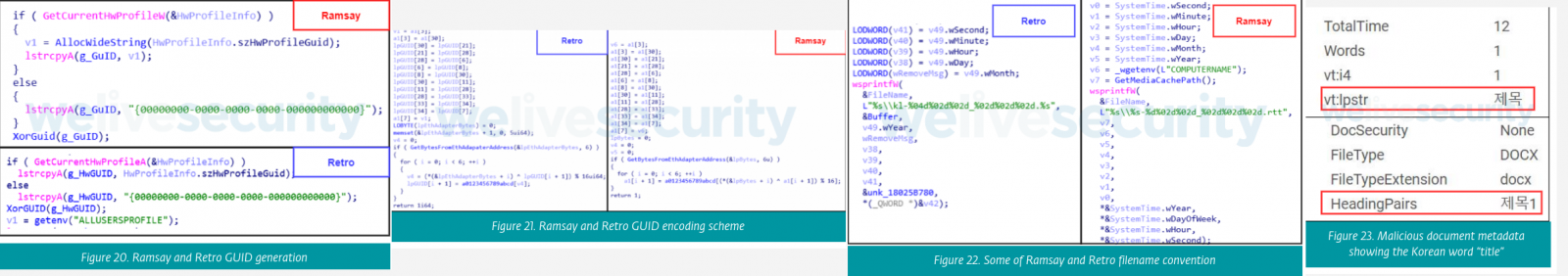
ESET discovered additional common ground between the two pieces of malware. According to their research, Ramsay and Retro use the same API to generate the unique identifier (GUID) for the infected machines and the same algorithm to encode it.
Additionally, both saved some log files following the same naming convention and relied on the same open-source tools for privilege escalation and for deploying some of their components.
On top of this, the malicious documents that delivered Ramsay contain language metadata in the form of the Korean word for “title.”
However, all this cannot be considered reliable evidence for a connection with DarkHotel.
ESET researchers believe that the adversary behind Ramsay has knowledge of the victim’s environment and is developing attack vectors that would preserve resources.
The information contained in this website is for general information purposes only. The information is gathered from Bleeping Computer, while we endeavour to keep the information up to date and correct, we make no representations or warranties of any kind, express or implied, about the completeness, accuracy, reliability, suitability or availability with respect to the website or the information, products, services, or related graphics contained on the website for any purpose. Any reliance you place on such information is therefore strictly at your own risk. Through this website, you are able to link to other websites which are not under the control of CSIRT-CY. We have no control over the nature, content and availability of those sites. The inclusion of any links does not necessarily imply a recommendation or endorse the views expressed within them. Every effort is made to keep the website up and running smoothly. However, CSIRT-CY takes no responsibility for, and will not be liable for, the website being temporarily unavailable due to technical issues beyond our control.