Microsoft on Monday published guidance for a newly discovered zero-day security flaw in its Office productivity suite that could be exploited to achieve code execution on affected systems.
The weakness, now assigned the identifier CVE-2022-30190, is rated 7.8 out of 10 for severity on the CVSS vulnerability scoring system. Microsoft Office versions Office 2013, Office 2016, Office 2019, and Office 2021, as well as Professional Plus editions, are impacted.
To help protect customers, Microsoft published and additional guidance here.
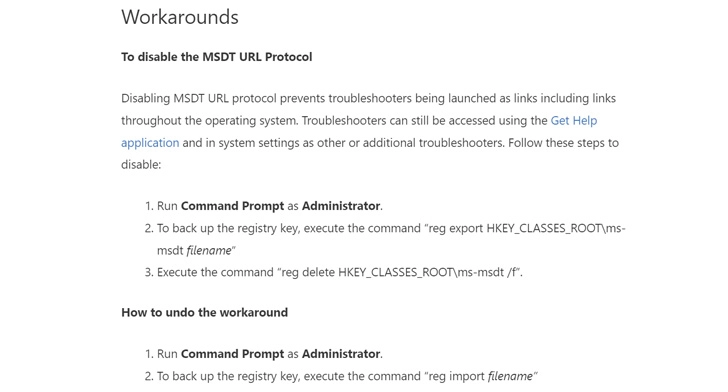
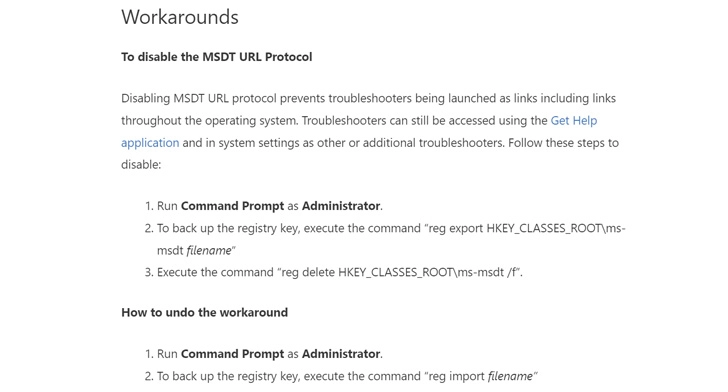
Besides releasing detection rules for Microsoft Defender for Endpoint, the Redmond-based company has offered workarounds in its guidance to disable the MSDT URL protocol via a Windows Registry modification.
The information contained in this website is for general information purposes only. The information is gathered from TheHackerNews, while we endeavour to keep the information up to date and correct, we make no representations or warranties of any kind, express or implied, about the completeness, accuracy, reliability, suitability or availability with respect to the website or the information, products, services, or related graphics contained on the website for any purpose. Any reliance you place on such information is therefore strictly at your own risk. Through this website, you are able to link to other websites which are not under the control of CSIRT-CY. We have no control over the nature, content and availability of those sites. The inclusion of any links does not necessarily imply a recommendation or endorse the views expressed within them. Every effort is made to keep the website up and running smoothly. However, CSIRT-CY takes no responsibility for, and will not be liable for, the website being temporarily unavailable due to technical issues beyond our control.